Windows Server
This document provides the steps required to configure the Windows Server Inspector.
Quick DetailsRecommended Agent: Self-Managed
Supported Agents: Self-Managed
Is Auto-Discovered By: Endpoint Agent Installation
Can Auto-Discover: Active Directory, SQL Server Inspectors, Hyper-V, Network Discovery, StorageCraft SPX
Parent/Child Type Inspector: No
Inspection via: CLI
Data Summary: Here
Overview
Endpoint Inspector CountThe Windows Server Inspector is an Endpoint Inspector. Endpoint Inspectors are billed per unit according to your agreement with Liongard. Usage beyond the contracted amount will be charged on your monthly invoices.
To view your Endpoint Inspector count per Environment, navigate to Admin > Environments > Review the "Endpoint Inspector" column
To view the number of included Endpoint Inspectors and your minimum commitment for Endpoint Inspectors, navigate to your username in the upper right-hand corner and select Company Settings.
Please contact your Account Manager for additional contract and pricing details.
See it in Action
The Windows Server Inspector supports Auto-Discovery.
Windows Server Inspector vs. Active Directory InspectorThe Windows Server Inspector pulls data for local accounts. Because Windows servers with the Active Directory role applied have no local users, that table will be blank.
To review data from accounts on the Active Directory domain, please use our Active Directory Inspector.
For more information on what data the Windows Server Inspector pulls, please review our System Inspector Summary document.
Network Discovery Inspector Auto-DiscoveryThe Network Discovery inspector can not scan a subnet larger than a /17 which totals 32,768 hosts. If the network found is larger than a /17, the Windows Server Inspector will not auto-discover a Network Discovery Inspector.
Inspector Setup Preparation
System RequirementsThe Windows Server Inspector requires a Windows Server 2016 or greater.
As of June 1, 2024, Liongard is ending support for Windows Server 2012 on agent versions 4.2.4 and greater. This comes as a result of Microsoft deprecating support for this operating system version as of October 13, 2023.
Liongard agent versions 4.2.4 and greater are now incompatible with Windows Server 2012 and lower, and partners may experience issues with inspections associated with these servers.
Partners still needing to inspect systems running Windows Server 2012 may continue to use agent version 4.2.3; however, this agent version has now reached End of Maintenance (EOM) and will reach End Of Life (EOL) effective May 31, 2025
Initial Setup on a New Network
Windows Server Inspectors will be auto-discovered by installing the self-hosted Windows Agent. To proceed, deploy the Windows Agent to all Windows Servers you want to inspect.
- If auto-activation is not turned on, activate and run the auto-discovered Windows Server Inspectors. In addition to landing data about that server, it will auto-discover an Active Directory Inspector if the server is an Active Directory domain controller. The Windows Server inspector will also auto-discover a Network Discovery Inspector. if a Network Discovery Inspector has not already been discovered or activated.
- The Network Discovery Inspector can discover several different types of network Inspectors, as detailed on the Network Discovery Inspector page.
- Note there will only be one Network Discovery Inspector auto-discovered per Environment.
Endpoint Inspector Auto-activation
If you want ALL Endpoint Inspectors to auto-activate after Auto-discovery, navigate to your Username > Company Settings and turn on the Endpoint Auto-Activation toggle as shown. After this toggle has been enabled, individual Environments can be excluded from the Endpoint auto-activation process by adding them to the list below the toggle.
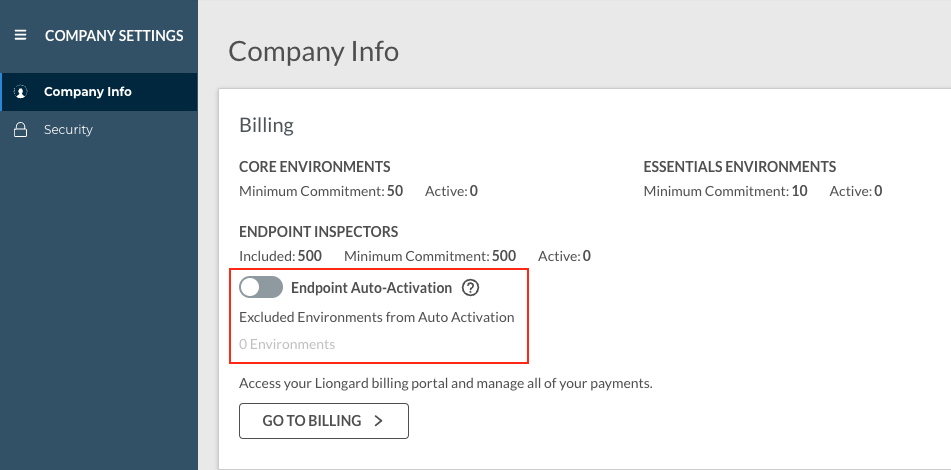
Please keep in mind that Endpoint Inspectors are billed per unit, and usage beyond your minimum commitment (also found on the Company Settings screen) will incur additional costs.
Enabling auto-activation means that Endpoint Inspectors will be automatically Auto-discovered, activated, and billed accordingly.
Optional: Turn on Flexible Asset/Configuration Auto-Updating
If you would like this Inspector's data to be sent to ConnectWise and/or IT Glue, turn on Flexible Assets/Configurations for this Inspector:
- ConnectWise: Admin > Integrations > ConnectWise > Configuration Types > Confirm the "Configuration Auto-Updating" toggle is enabled
- IT Glue: Admin > Integrations > IT Glue > Flexible Assets > Confirm the "Flexible Asset Auto-Updating" toggle is enabled
Warranty Information
The Windows Server Inspector will surface warranty data for Dell and Lenovo servers. Warranty information for Dell and Lenovo workstations can be found on the "Warranty" Data View tab. Every 7 days after 1st inspection date we run a lookup for warranty expiration date to see if there has been any updates.
Liongard is still working on including warranty data for other manufacturers. If the Windows Server Inspector runs against a machine that is not Dell or Lenovo, the Warranty Data View tab will not be visible.
Auto-Discovery: Active Directory, Hyper-V, and SQL Server
The Windows Server Inspector Auto-Discovers Active Directory, Hyper-V, Network Discovery, and SQL Server Inspectors.
To set up an Auto-Discovered Active Directory, Hyper-V, and/or SQL Server Inspector(s), please see our Active Directory Inspector, Network Discovery Inspector., Hyper-V Inspector, and/or SQL Server Inspector documentation.
Windows Server Quick Tips/FAQs
Updated 8 months ago
